Over the last few days the issue on how to prevent users to create Office 365 Groups has popped up in all sorts of conversations. This blog post will show you how to do it in the correct way, and serve as a future reference. I’m not the only one who have blogged about this, it’s in many places including official documentation. But in many places both scripts and some caveats are either wrong or outdated. One post covers this topic really well, and in a good and correct way and it’s this post by John P. White - Disable Office 365 Groups, part 2. Read it! This post however will show you how to do it in a more direct way, using PowerShell.
Background
We used to prevent end-users from creating Office 365 Groups (from now on referred to as only Groups) using an OWA Mailbox policy. Even I have a blog post on that topic. But this way to do it is outdated. That mailbox policy only applies to Groups being created from OWA (Outlook Web Access, Outlook on the web…whatever) and Outlook. It did not prevent people from creating Groups using Microsoft Teams, Planner, StaffHub, PowerBI, Dynamics 365 and what not.
How to do it properly
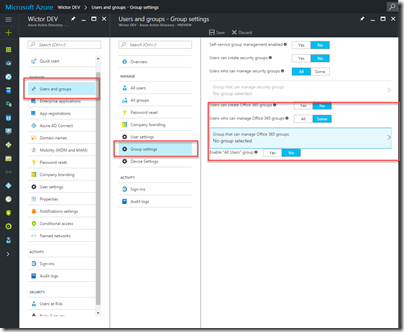
Instead of continuing to building the settings on the Mailbox policy setting, this setting has now moved to Azure AD. You can even see it in the “new” Azure Portal, although it doesn’t really reflect the real settings and not all settings.
The way to do it is to use PowerShell and essentially follow the official documentation. The problem with that article however is that it contains a few errors, is not updated, has some weird scripts and is just to darn long to read through. So, here’s a my PowerShell for this. You can find the complete script in this Gist.
Prerequisites
To be able to run the PowerShell you need to install some stuff
- The Microsoft Online Services Sign-in assistant
- The Windows Azure Active Directory Module for PowerShell - and here’s a big thing. You MUST (at the time of writing) only use the preview version, with version number 1.1.130.0-preview found here. Do not try to download the higher version with version number 1.1.166.0 - it will not work.
Now, we got that out of the way, let’s get to the fun stuff.
Scripting FTW
First we need to log in to our tenant using an admin account. I prefer to use a the Get-Credential method over the dialog option, makes everything more smoother.
# Store the credentials in a variable
$creds = Get-Credential
# Connect to the Microsoft Online services
Connect-MsolService -Credential $creds
The next thing is to make sure that users are allowed to create Groups, we’ll limit it later. Make sure you use the script below and not the one in the official article as they have spelling errors on the variable.
# Get tenant setting (misspelled in official docs)
Get-MsolCompanyInformation | Format-List UsersPermissionToCreateGroupsEnabled
# If false, then use the following
Set-MsolCompanySettings -UsersPermissionToCreateGroupsEnabled $true
To limit the users allowed to create Groups we need to have a security group with members in Azure AD. And we need the Id of that group, so we’ll grab it with some PowerShell:
# Retrieve ID of Group that should have the option to create groups
$group = Get-MsolGroup -SearchString "Group creators"
The settings we need to set are contained in an Azure AD object, created from a template. We retrieve that template using the following command and create our settings object like this:
# Retrieve the Group.Unified settings template (assuming you have not done this before)
$template = Get-MsolAllSettingTemplate | Where-Object {$_.DisplayName -eq "Group.Unified"}
# Create the settings object from the template
$settings = $template.CreateSettingsObject()
Once we have the settings object, we can start setting properties.
- EnableGroupCreation - should be set to false. We negate the tenant setting here, and we’ll override it soon again for the specific security group
- GroupCreationAllowedGroupId - this is the Id of the security group that are allowed to create Groups
- UsageGuidelinesUrl - a URL pointing to your usage guidelines. Optional, but recommended
- GuestUsageGuidelinesUrl - a URL pointing to usage guidelines for external users. This link will be shown in the external sharing e-mails and should of course be on a public available location. Optional, but recommended
- ClassificationList - a comma separated list with your classification labels. Optional. Currently the first one in the list will be the default one. (does not work in all tenants at the time of writing)
There’s some more properties that you can take a look at, and over the last few weeks even some more popped up (without any documentation).
# Use this settings object to prevent others than specified group to create Groups
$settings["EnableGroupCreation"] = $false
$settings["GroupCreationAllowedGroupId"] = $group.ObjectId
# (optional) Add a link to the Group usage guidelines
$settings["UsageGuidelinesUrl"] =
"https://contoso.sharepoint.com/Pages/GroupUsageGuidelines.aspx"
# (optional) Add a link to Guest usage guidelines
$settings["GuestUsageGuidelinesUrl"] =
"http://contoso.com/usageguidelines"
# (optional) Add classifications to be used for Groups
$settings["ClassificationList"] = "Public,Internal,Top Secret"
# Verify
$settings.Values
Now we have the settings and all we need to do is to add them to Azure AD:
# Add the settings to Azure AD
New-MsolSettings -SettingsObject $settings
And from now on, only members of the security group can create Office 365 Groups using all endpoints such as Planner, Teams, PowerBI, Microsoft Graph REST etc. BUT StaffHub still ignores this setting!!!!! Aaargh!
Need to update the settings?
If you need to update the settings, or there are new properties that you want to configure, then use the PowerShell below. The one(s) in the official documentation is really weird written…
# Retrieve settings
$settings = Get-MsolAllSettings | Where-Object {$_.DisplayName -eq "Group.Unified"}
# Check the values
$settings.Values
# Update a property
$settings["GuestUsageGuidelinesUrl"] = "http://www.wictorwilen.se"
# Save the updates
Set-MsolSettings -SettingId $settings.ObjectId -SettingsValue $settings.GetSettingsValue()
Summary
That’s it. It’s not rocket science. Looking forward to further settings and also a proper UI in the Azure portal for the lazy people.
The PowerShell is a bit weird though, should have had a review by the PowerShell team before going into the production in my opinion.